Recent searches
Search options
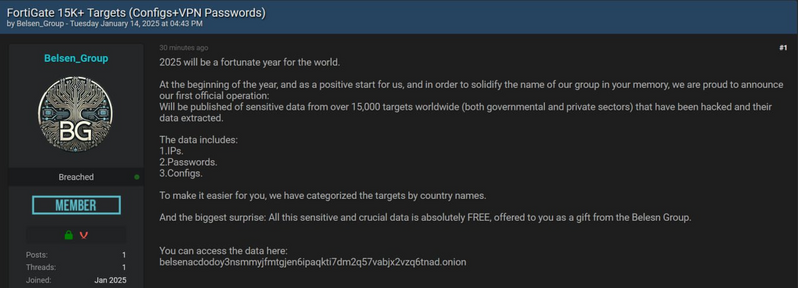
A new group, Belsen Group, claim to have released Fortigate configs for 15k firewalls.
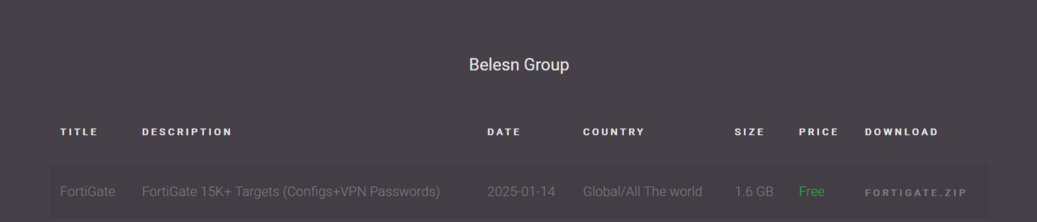
The ZIP contains a folder for each IP address, inside is config.conf (Fortigate full config dump) and vpn-passwords.txt.
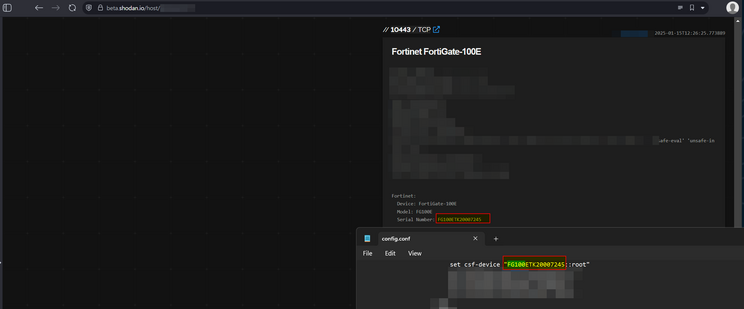
The Fortigate config data appears legit - they're unique - and it looks like a very serious cyber incident is going to play out. Some align to Shodan.
All the configs appear to come from Fortigate 7.x devices, so this is probably the latest zero day Fortinet didn't tell people about (edit: update in thread, some are 7.2.x devices).
In terms of validity, you can directly match up devices between the IPs and config.
The VPN usernames and passwords are in plain text. There's also the device certs etc.
A small number of the devices are on Fortigate 7.2, versions from late 2022 - which tends to blow the recent CVE out of the water as that's not supposed to be impacted.
I've confirmed one of the usernames and passwords with one of the victims a friend works at. Impacted orgs are going to need to change local SSL VPN passwords, admin passwords etc.
If anybody wonders if it's related to this prior Fortigate SSL VPN dump: https://www.bleepingcomputer.com/news/security/hackers-leak-passwords-for-500-000-fortinet-vpn-accounts/
I don't think so. The configs run to a year later version wise, and the IP addresses in that dump don't align with this dump.
The other thing to mention is the prior dump was via CVE-2018-13379. These devices, based on the config dumps, are largely running versions which were long ago patched for that.
So what = later vuln.
Off to bed now, plan for later on tomorrow is to publish the impacted IPs so orgs have a chance to know if they're in scope.
The last time somebody did this, it was a ransomware group as basically a freebie to attract operators.
Regarding 'the data's old':
a) the version numbers run up to 2 years ago, that's not very old
b) many of the devices are still online and reachable
c) there's data in the dump which has not been published before as far as I can see, along with device configs
One final update - did some IR on an impacted device, it looks like CVE-2022-40684 based on artefacts left behind.
It also looks like the data was assembled in October 2022 and only just released, looking back at historic IP records vs the dump. So basically if your config might be in the dump even if you patched, as it was a zero day at the time.
Also in the dump is complete firewall rules for the devices.
1.30am bloggo I wrote
Everything I know about the Fortigate config dump situation
Also, Belsen was a exchange camp, where Jewish hostages were held with the intention of exchanging them for German prisoners of war held overseas.
GitHub repo with the FortiGate config dump IPs. If you’re on this list, you need an incident to rotate creds etc.
https://github.com/arsolutioner/fortigate-belsen-leak/blob/main/affected_ips.txt
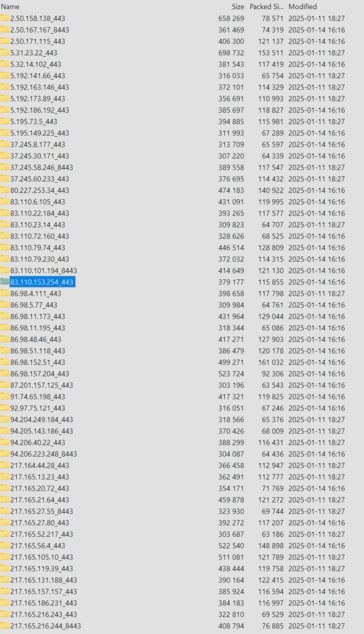
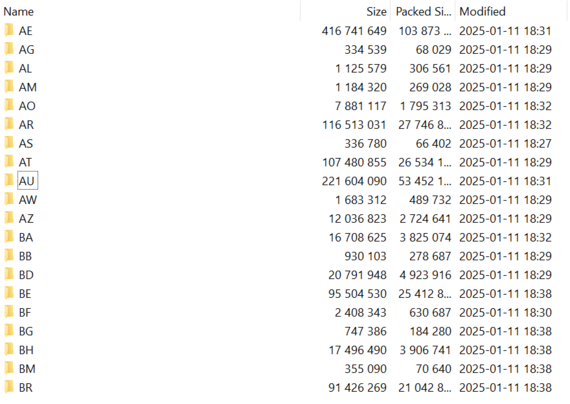
Here's how the data was organised, by country (Australia and UAE love Forti).
The data appears to have been assembled for release starting on the 11th, based on the modified dates (but was collected years earlier).
Thanks for all of this, as ever. Wondering if anyone pulled all of this down and re-uploaded the full dataset anywhere as the original appears to be down?