Recent searches
Search options
Rackspace say there is a zero day in ScienceLogic EM7, which has been exploited inside Rackspace.
https://x.com/ynezzor/status/1839931641172467907
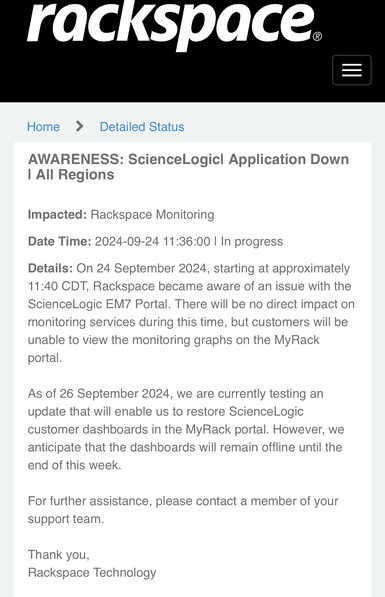
Rackspace outage report from 24th September 2024 (doesn't mention a security incident): https://rackspace.service-now.com/system_status?id=detailed_status&service=4dafca5a87f41610568b206f8bbb35a6
ScienceLogic haven't got anything on their support site about a new vulnerability.
The Register has picked up this story.
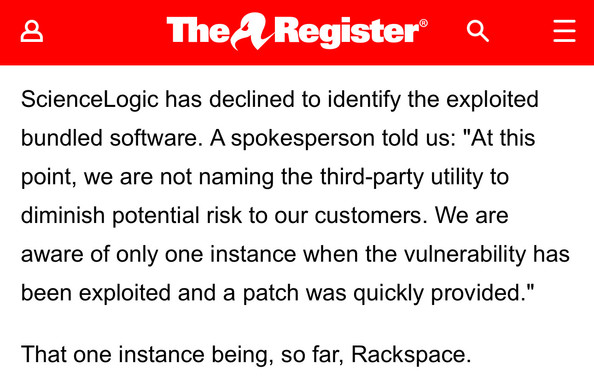
Sciencelogic say the vulnerability is in a third party software library and no CVE has been issued, and they’re declining to name the library.
One to watch. Smells of dead bodies in cupboards. https://www.theregister.com/2024/09/30/rackspace_zero_day_attack/
Sciencelogic have published a security update for ScienceLogic SL1 which fixes the zero day vulnerability.. but they’ve put it behind a paywall, haven’t told customers and haven’t issued a CVE. #Rackspace #threatintel #ScienceLogic
PSA for ScienceLogic SL1 customers - go to the support portal and download and apply the security hotfix for the product.
They haven't told people to do this and haven't allocated a CVE and locked it behind a support paywall -- but there's an actively exploited zero day in the product they're trying to actively downplay. #Rackspace #threatintel #ScienceLogic
Does anybody know which third party application within ScienceLogic is the vulnerable one?
ScienceLogic are refusing to disclose, as are Rackspace, so it’s created this ridiculous situation where there’s an actively exploited zero day in the wild where there’s zero information on how to protect and detect.
My Signal address is in my profile.
I have a fun blog about the ScienceLogic situation due to drop on Monday entitled “ScienceLogic and their security vulnerability cover ups”. #Rackspace #threatintel #ScienceLogic
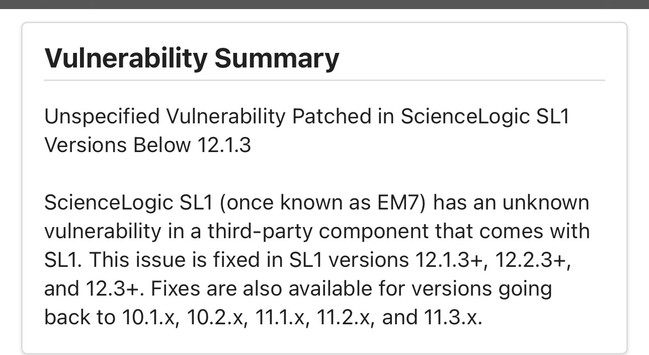
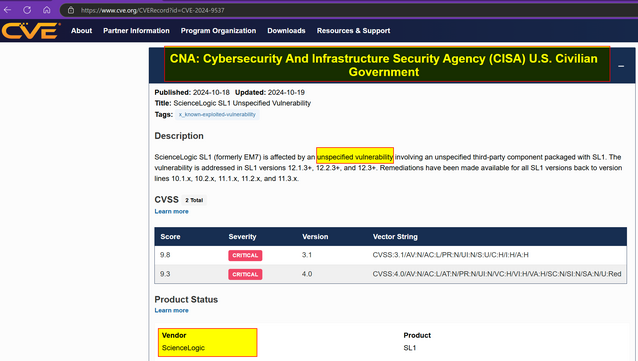
A CVE has been allocated for the ScienceLogic ‘third party application’ zero day that lead to the Rackspace breach. CVE-2024-9537
Patches have been made available finally.
The articles for it are all behind a paywall on ScienceLogic portal.
The vulnerability description is an “unspecified vulnerability”.
Friday night dump.
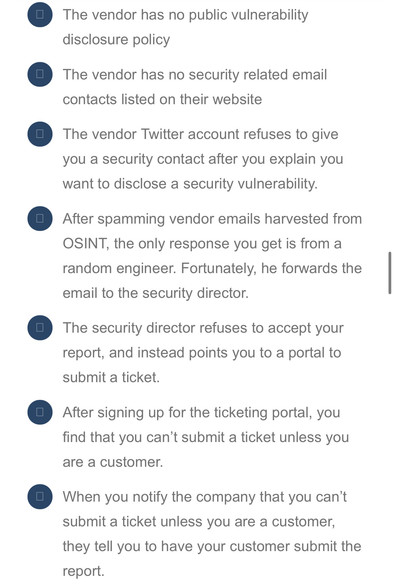
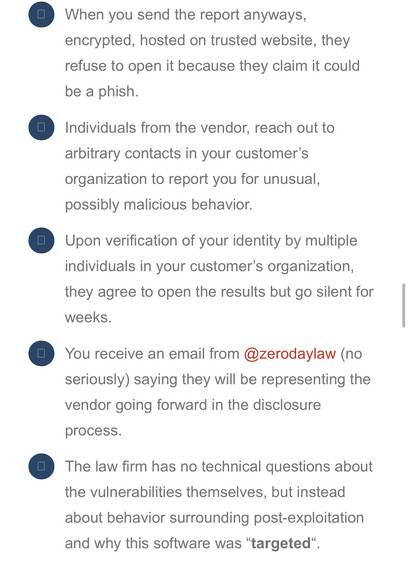
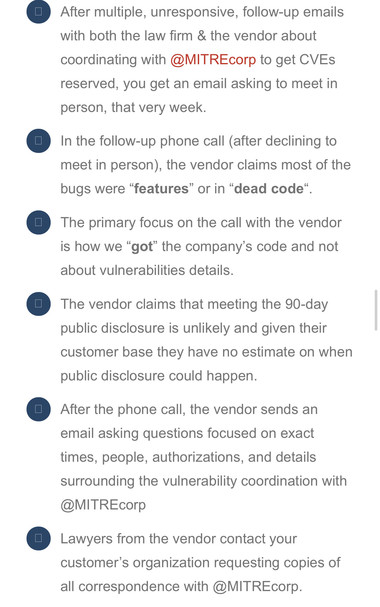
Previously on ScienceLogic - the time last year where they threatened legal action during a vulnerability report via MITRE. https://web.archive.org/web/20230816081531/https://www.securifera.com/blog/2023/08/16/sciencelogic-dumpster-fire/
Aside from having one of the worst vulnerability disclosure processes from any vendor, ScienceLogic also now has a CVE allocated by... CISA.
Maybe they can make legal threats to the USG this time... or hire some security people. https://www.cve.org/CVERecord?id=CVE-2024-9537
Additional updates coming on the ScienceLogic saga. I think they've lied about the nature of the vulnerability.
@GossiTheDog Me: “What the fuck is this thing? Some kind of PLC used in biotech?”
The website: See everything across multi-cloud and distributed architectures, contextualize data through relationship mapping, and act on this insight through integration and automation.
Me: “Okay, buzzword salad with an AIOps dressing.”
My condolences to whomever had this foisted upon them.
@GossiTheDog ‘It wasn’t us. It was some other thing that magically comes wrapped with our thing, so blame that other thing’.
@GossiTheDog My guess is they'll make the legal threats first.
@GossiTheDog By that you mean: it isn't in a third-party component?
Also, this practice of keeping security advisories behind a paywall is maddening.